10 things you should know about containerization technology
Linux containers have been around since the early 2000s and architected into Linux in 2007. Due to the small footprint and portability of containers, the same hardware can support an exponentially larger number of containers than VMs, dramatically reducing infrastructure costs and enabling more apps to deploy faster. But due to usability issues, it didn’t kickoff enough interest until Docker (2013) came into the picture. To name a few prominent container platforms now – Docker, Kubernetes, Cloud Foundry, etc.,

Image – Mesosphere
- Linux containers, contain applications in isolated fashion to keep them isolated from the host (OS) system that they run on.
- Containers allow a developer to package up an application with all of the artifacts it needs, such as libraries and other dependencies, and ship it all out as one package.
- It provides a consistent experience as developers and system administrators move code from development environments into production in a fast and replicable way.
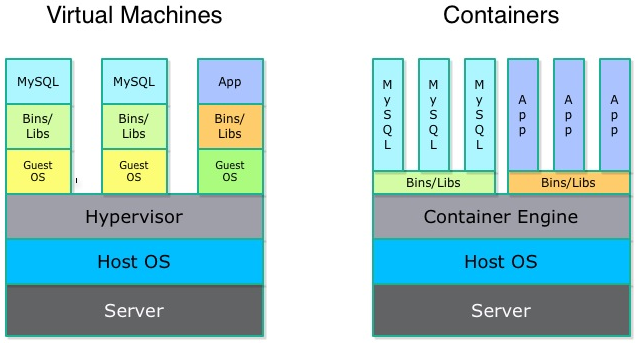
- Containers don’t need to replicate an entire operating system, only the individual components they need in order to operate. This gives a significant performance boost and reduces the size of the application. They also operate much faster, as unlike traditional virtualization the process is essentially running natively on its host.
 Image – LXC
Image – LXC - Containers have also sparked an interest in microservice architecture, a design pattern for developing applications in which complex applications are broken down into smaller, composable services work together. Each component is developed separately, and the application is then simply the sum of its constituent components. Each service can live inside of a container, and can be scaled independently of the rest of the application as the need arises.
- A bit about Docker platform: Its a utility designed to make it easier to create, deploy, and run applications by using containers. It is designed to benefit both developers and system administrators, making it a part of many DevOps (developers + operations) toolchains(set of distinct software development tools that are linked). For developers, it means that they can focus on writing code without worrying about the system that it will be running on. Containers allow a developer to package up an application with all of the artifacts it needs, such as libraries and other dependencies, and ship it all out as one package. The developer can be rest assured that the application will run on any other Linux machine regardless of any customized settings that machine might have that could differ from the machine used for writing and testing the code. For operations staff, Docker gives flexibility and potentially reduces the number of systems needed because of its small footprint and lower overhead.
- Docker is different from standard virtualization, it is operating system level virtualization. Unlike hypervisor virtualization, where virtual machines run on physical hardware via an intermediation layer (hypervisor), containers instead run user space on top of an operating system’s kernel. That makes them very lightweight and fast.
- Benefits of Containers :
- Isolating applications and operating systems through containers.
- Providing nearly native performance as container manages allocation of resources in real-time.
- Controlling network interfaces and applying resources inside containers.
- Limitations of containers :
- All Containers are running inside the host system’s Kernel and not with a different Kernel.
- Only allows Linux “guest” operating systems.
- Container is not a full virtualization stack like Xen, KVM, or libvirt.
- Security depends on the host system hence containers are not secure.
- Risks due to containers :
- Container breakout: If any one of the container breaks out, it can allow unauthorized access across containers, hosts or data centers etc., thus affecting all the containers hosted on the Host OS.
- There could DDOS and cross-site scripting attacks on public facing containers hosted applications.
- A container being forced to use up system resources in an attempt to slow or crash other containers.
- If any of the compromised containers attempting to download additional malware, or scan internal systems for weaknesses or sensitive data, this can affect all the hosted containers.
- Use of unsecure applications to flood the network and affect the other container.
In the coming weeks, we can learn more about different container platforms. If I have missed out anything, please post it in the comments section.
Like this post? Don’t forget to share it!
Additional Resources :
- Implementing secure containers using gVisor+Docker tutorial
- Take look at Podman, Red Hat’s daemon-less Docker Alternative
Summary

Article Name
10 things you should know about containerization technology
DescriptionIn this post,we take look at 10 things you should know about containerization technology
Author
Karthik
Publisher Name
upnxtblog
Publisher Logo


Average Rating